Introduction
In today digital world,111.190 l.150.255 every device connected to the internet has a unique identity known as an IP address. One such address that often appears in logs, security tools, and network reports is (sometimes mistakenly written as 111.190 l.150.255 At first glance, it may look like a random number, but in reality, it is part of a highly structured global internet system that controls how data moves across networks.
Many people search this IP address after seeing it in firewall logs, website analytics, cybersecurity alerts, or even suspicious traffic reports. This creates curiosity and sometimes concern: Is it dangerous? Is it a hacker? Is it a virus? Or is it just normal internet traffic?
This article will break down everything in detail in a simple, human way. You will learn what 111.190.150.255 really is, where it comes from, how IP tracking works, whether it is safe or suspicious, and how cybersecurity experts analyze such addresses in real-world situations.

What is 111.190.150.255? Understanding the Core Meaning
The IP address111.190 l.150.255 is part of the IPv4 system, which is the foundation of modern internet communication. IPv4 uses a 32-bit structure divided into four numerical blocks separated by dots. Each block can range from 0 to 255, which is why this format looks like a sequence of numbers.
This specific IP belongs to a larger network block often grouped as 111.190.150.0/24, meaning it represents a range of 256 possible IP addresses controlled under one network allocation. According to global IP database records, this range is associated with internet service infrastructure rather than a single personal device.
In simple terms, this IP is not a person or a device—it is a network identifier used to route internet traffic between servers, websites, and users.
How IP Addresses Like 111.190.150.255 Work in the Internet System
To understand this IP properly, we need to understand how the internet actually works. Every time you open a website, send a message, or stream a video, your device communicates using IP addresses.
When data is sent online, it is broken into small packets. Each packet contains a “from” IP and a “to” IP. The address111.190 l.150.255 can appear in this process as part of routing, server communication, or background network activity.
Modern systems like ISPs (Internet Service Providers) and cloud networks manage millions of such IP addresses simultaneously. These IPs help direct traffic efficiently across global networks, ensuring that data reaches the correct destination without confusion.
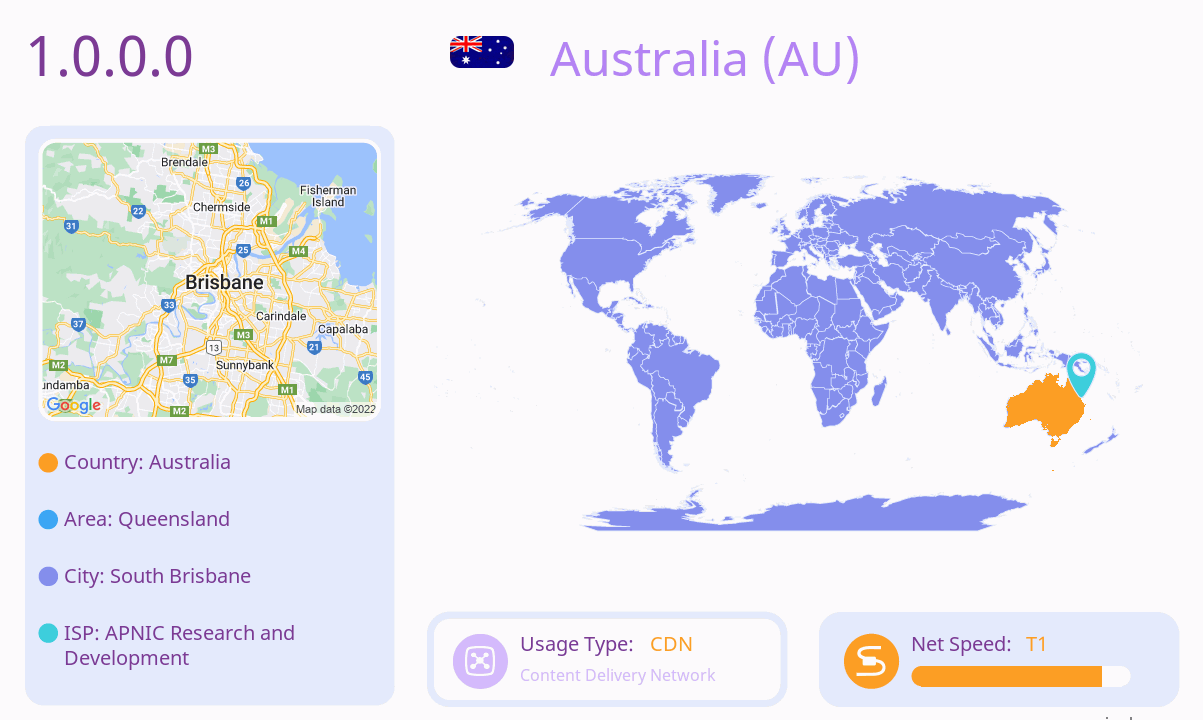
Geolocation of 111.190.150.255 and What It Really Means
One of the most searched aspects of any IP address is its location. IP geolocation tools estimate where an IP is likely registered based on ISP data and network allocation records.
For public IP database sources suggest it belongs to a large ISP-managed range associated with Japan-based network infrastructure (SoftBank-related IP blocks).
However, it is extremely important to understand that IP geolocation is NOT exact. It does not show a street address, house, or individual. Instead, it shows:
The ISP registration region
The network hub location
The data center or routing node
This is why cybersecurity experts always treat IP location as an estimate, not proof of identity.
Why 111.190.150.255 Appears in Logs and Website Analytics
Many users first notice this IP in server logs, firewall dashboards, or analytics reports. This can create confusion or fear, especially when it appears repeatedly.
In reality, there are several normal reasons for this:
It may be a server request from a hosting network
It may be automated bot traffic from a data center
It may be part of CDN (Content Delivery Network) routing
It may be background scanning or indexing activity
Modern websites constantly interact with multiple IP addresses at once. Some of these are harmless system processes, not human users.
That is why cybersecurity professionals never judge an IP based only on appearance—they analyze behavior patterns instead.
Is 111.190.150.255 Safe or Dangerous? Cybersecurity Perspective
From a cybersecurity standpoint, an IP address alone cannot be labeled as “safe” or “dangerous.” It depends entirely on behavior, frequency, and context.
Most IPs in large ISP ranges like 111.190 l.150.255 are part of shared infrastructure. This means thousands of users or systems may use similar addresses for legitimate purposes.
Security systems only flag an IP when it shows suspicious behavior such as:
Unusual traffic spikes
Repeated failed login attempts
Bot-like activity patterns
Spam or automated requests
Without these indicators, the IP is generally considered normal internet traffic.
IP WHOIS Data and What It Reveals About 111.190.150.255
WHOIS data is one of the most important tools used to analyze IP addresses. It shows the organization responsible for managing an IP block.
For 111.190 l.150.255, WHOIS and IP registry data typically reveal:
Assigned ISP organization
Network block ownership
Regional allocation information
Abuse contact details
These records confirm that the IP belongs to a structured internet service provider network rather than an individual user device.
However, WHOIS does NOT reveal personal data like names, phone numbers, or home addresses. This is protected for privacy reasons under global internet policies.
Why IP Addresses Are Not Enough to Identify Individuals
One of the biggest misconceptions in cybersecurity is assuming an IP address can identify a person. In reality, IP addresses like 111.190 l.150.255 cannot directly reveal personal identity.
There are several reasons for this:
Many users share the same IP (NAT systems)
IP addresses change frequently (dynamic allocation)
VPNs and proxies hide real locations
ISPs store private user mapping internally
Even law enforcement requires ISP cooperation to trace an IP to a person, and this process involves legal procedures—not direct lookup.
This is why experts always say:
An IP shows a network, not a person.
Cybersecurity Risks and Misuse Possibilities
While 111.190 l.150.255 itself is not harmful, any IP can be involved in malicious activity depending on usage.
Cybersecurity systems monitor IP behavior to detect threats like:
Botnet activity
Spam distribution
DDoS attack traffic
Unauthorized scanning attempts
If an IP is repeatedly flagged across global security databases, it may be added to threat intelligence lists.
However, most large ISP IP ranges naturally contain mixed traffic—both legitimate and automated—so false positives are common.
This is why professional security analysis uses multiple signals, not just IP reputation.
The Role of IP Tracking Tools and Modern Digital Forensics
Today, IP tracking is a major part of cybersecurity, digital marketing, and network diagnostics. Tools like IP lookup services and threat intelligence platforms analyze addresses such as 111.190 l.150.255.
These tools provide:
ISP identification
ASN (network owner details)
Approximate geolocation
Traffic behavior classification
Security risk scoring
According to geolocation technology standards, IP mapping also includes latitude/longitude estimation, region mapping, and network routing analysis.
However, professionals always emphasize that these results are probabilistic, not absolute.
Why This IP Is Part of a Larger Internet Infrastructure
111.190 l.150.255 is not an isolated entity. It is part of a much larger system of internet routing that includes thousands of similar IP blocks.
These blocks are used by ISPs to:
Manage broadband users
Run mobile data networks
Operate enterprise systems
Support cloud infrastructure
This means the IP is likely part of a backbone network that handles massive amounts of global internet traffic every second.
Such IP ranges are essential for maintaining internet stability and connectivity across countries and continents.
Final Conclusion
The IP address 111.190.150.255 is a structured part of the global IPv4 internet system, not a personal identifier or a standalone threat. It belongs to a larger ISP-managed network range and is used in routine internet routing, server communication, and digital infrastructure operations.
Although it may appear in logs or security reports, it does not automatically indicate danger or malicious activity. IP geolocation shows only approximate regional data, and WHOIS records confirm network ownership—not personal identity.
Understanding how IP addresses work helps users avoid misinformation and unnecessary fear. In modern cybersecurity, context is everything. An IP like 111.190.150.255 should always be analyzed through behavior, patterns, and network intelligence—not isolated assumptions.